DIRECTORS

Mrs. Oluseyi A. Ogundowo
Military Agencies Department

Mrs. Eucharia N. Ugwu
Higher Education Audit Department

Mr. Andrew O. Onwuidili
Extra-Ministerial Audit Department

Mr. Gabriel Gbayan
Health & Allied Institute Audit Department

Mr. Gandu Magaji Andrew
Judiciary Audit Department

Mr. Ogbonna Ubah Peter
Performance Audit Department

Mrs. Nwadike Nwamaka Christiana
Ministerial Audit Department

Mr. Akindele Wasiu Dolamu
Environmental Audit Department

Mr. Angbo Benjamin Yakwo
Inspectorates Audit Department
Mr. Vandu Ngaduna John
States Department

Mr. Anugwa Chinwendu Jonathan
Treasury Audit Department

Mrs. Akinlabi-Raji Morenike Sherifah
Education Research Institution Audit Department

Dr. Olaleye Idowu
Health Research Institutes Audit Department

Mrs. Ibikunle Taiwo Asanat
Police Affairs Audit Department

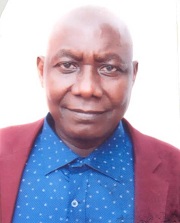
Mr. Adenuga Peter Olufemi
Emerging Issues Audit Department




